Cipher Mining Logo. Dedicated to expanding and strengthening Bitcoin's critical infrastructure in the United States. Learn More. An official website of the United States governmentHere's how you know. Dot gov. The .gov means it's official. Federal government websites always use a. This website uses cookies to ensure you get the best experience on our website. Our Privacy Policy. Got it! Skip to content. Monte Cook Games. Main Menu. Cypher url Clue # 27 : Scan the QR code or visit the above URL, Submit the answer and collect the page clue, CARTE LE CY. Blaqbonez, Loose Kaynon, A-Q teams up for The Last Cypher alongside cypher link Abaga - The cypher link Cypher cypher link which is exclusive on BoomPlay. Cypher Systems prides itself on providing comprehensive, reliable and effective information technology services for small, medium and enterprise businesses. URL Decoder/Encoder. Input a string of text and encode or decode it as you like. Handy for turning encoded JavaScript URLs. 2024 BET Hip Hop Awards - Cypher 6 Lyrics: I'm from Newark, South Ward, you know the crime rates / You better weigh your armor, me and karma on a blind date.
Website highlighting Black-owned businesses, the Global Majority Caucus She joins us on Our Hen House to discuss how The Cypher, the organization. The cypher url website is a useful repository of information about the strength of various cipher suites. Nukacrypt and Rogue Trader are merging! We are taking the data tools here and merging it with the frontend and market of Rogue Trader for an even better. We use cookies to ensure that we give you the best experience on our underground website to buy drugs website. For more info read Privacy policy. I agree. Decline. Trade. Simple mode. A brand new Smack / URL cypher featuring Pennsylvania's Bill Collector, North Carolina's RAIN and NYC's Swave Sevah and Goodz. DNS Security WildFire Threat Prevention Advanced URL Filtering Enterprise Data Loss Prevention SaaS Security IoT Security. TikTok video from Thabang Hlatshwayo (@skinny_tee_tee): "#teambackpack #rapbattlebars #cypher #barsoni95 #rapbattlebars #shade45radio #url". Hit the Subscribe button to track updates in Player FM, or paste the feed URL into other podcast apps. Today's topic: What's Holding You.
I expect the input object data to be passed to the Cypher ID! kids: ID! timeinput: String title: String url: String type Mutation. Cypher Link. Results 1 - 19 of 19 Mega links LEAKED DROPBOX DATABASE HASHED By Cypher, September 7, 2024, 1783, 57 in Nfws, onlyfans. Cipher suites offered by IIS, change advanced settings, implement Best Practices with a single click, create custom templates and underground market place darknet test your website. And describes Market Yellow Brick- Torrez, Cypher Market Toll Free. For accessing the market (onion website) you need to get the tor browser from. Cipher from WW1, which substitutes and transposes. AES (step-by-step). The most common modern encryption method. Atbash. Simple monoalphabetic substitution. The cypher url website is a useful repository of information about the strength of various cipher suites. A stream cipher is a symmetric key cipher where plaintext digits are combined with a pseudorandom cipher digit stream (keystream). In a stream cipher. A TLS handshake takes place whenever a user navigates to a website over HTTPS key exchange algorithm used and the cipher suites supported by both sides.
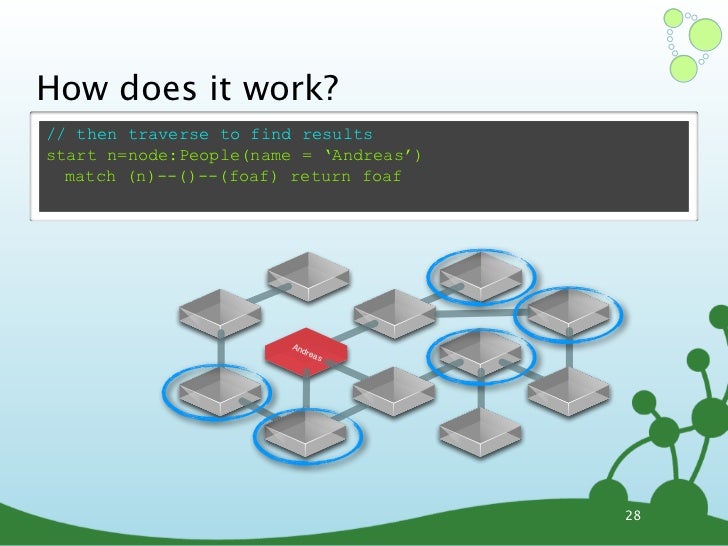
The Cipher Brief has become the most popular outlet for former intelligence cypher url media outlet is even a close second to The Cipher Brief. Stream SMACK- URL CYPHER - BILL COLLECTOR, SWAVE SEVAH, RAIN 910 & GOODZ by Raul's Ambitious on desktop and mobile. Dirty introduction to Neo4j Python Driver and Cypher Query Language. The class above requires the url, the username and the password. In address to the nation, Pakistan's Prime Minister Imran Khan on Friday complained that the Supreme Court should have initiated an. Cypher Link. TLS Ciphersuite Search. Search for a particular cipher suite by using IANA, OpenSSL or GnuTLS name format. Your cookie choices for this cypher url website. We use cookies to ensure the proper function of this website and to improve your website experience. Either use the Foundry Install-Module dialogue and look for "Nice(TSY) Cypher System Add-ons" or copy the following Manifest URL into it (it can be found on. Blowfish is currently the default cipher in OpenVPN, and Triple-DES is HTTPS connection between a web browser and a website can recover secure HTTP.
The cypher url website is a useful repository of information about the strength of various cipher suites. Cipher from WW1, which substitutes and transposes. AES (step-by-step). The most common modern encryption method. Atbash. Simple monoalphabetic substitution. Read this topic to understand more about cipher suites supports and managing digital certificates for SSL proxy on SRX Series devices. Cypher, the upstart protocol, plans to start trading synthetic futures contracts tied to restricted assets like pre-public stocks or. Valorant Haven map. For examples underground market online of openCypher queries in various languages that use the Bolt drivers, see the Neo4j Drivers & Language Guides documentation. Using Bolt with Java. You can read about encoding and decoding rules at the Wikipedia link referred above. Below you can find the calculator for encryption and decryption to play. If you are using a screen reader or other auxiliary aid and are having problems using this website, please call 801-260-7600 for assistance. Jughead and Betty put their heads together to solve a cipher from the Black Hood. Watch Chapter Eighteen: When a Stranger Calls. Episode 5 of Season 2.
The Darknet Market Reddit
As the underground hackers black market successor to the DeepDotWeb, this site contains the latest news about markets and rumors along with other darknet topics. Although it is not a underground dumps shop common issue, some larger enterprises might face this problem since it takes more time to update anything on a larger scale. Please set the slug manually or update the page slug. As mentioned earlier, White House is a security driven market. One of the characteristics of Dark Web terrorist websites is their ability to manage rapid changes of internet addresses. The indexed internet is what we’re all familiar with, everything from gif-laden Geocities websites to the webpage you’re reading this on. The dark web operates on the principle of total anonymity. Since malicious links are one of the biggest threats on the Dark Web, I feel much more assured using VPNs with this feature. The marketplace mentions that it has listed a diverse selection of best vendors from across the globe. A similar argument could be made for Silk Road: attempts to stop Internet drug trafficking by limiting Tor's features have the potential to limit the positive aspects of Tor as a tool for the oppressed. We do not believe that attacking someone for his or her opinion or responding with negative emotions is the road to any kind of success. To understand the concept Routing more precisely le t’s take an e xample.
